non-visible data.
visible trust.
NVD
non-visible data
Non-Visible Data (NVD) is our answer to the increasing complexity of modern IT environments. With NVD, security is not an add-on, but is embedded directly into the data itself. Information appears externally as random character strings – useless to attackers, yet always available to authorized users. Invisible to third parties, easy to use, efficient to integrate.
Invisible Data,
Visible Benefits
While traditional encryption protects data, it often makes it difficult to use. This is precisely where NVD comes in: Our technology makes data invisible – and at the same time efficiently shareable. The difference is that you don’t hand over copies; instead, you retain full control. For unauthorized parties, everything remains ‘noise,’ while authorized users gain access – but only for as long as the data owner permits. Key management works in a completely new way: there are no piles of keys, no exchange, no dependencies. Keys are calculated on demand and disappear immediately once they are no longer needed.
More Protection,
No Barriers
Traditional security approaches often create a conflict of objectives: the more secure, the more restricted the communication (security silos). NVD resolves this dilemma. The technology enables secure collaboration across systems, organizations, and borders – without additional interfaces, without loss of efficiency. This transforms security from an obstacle into an enabler: protection is no longer a barrier, but an integral part of the data infrastructure.
Protection through Invisibility
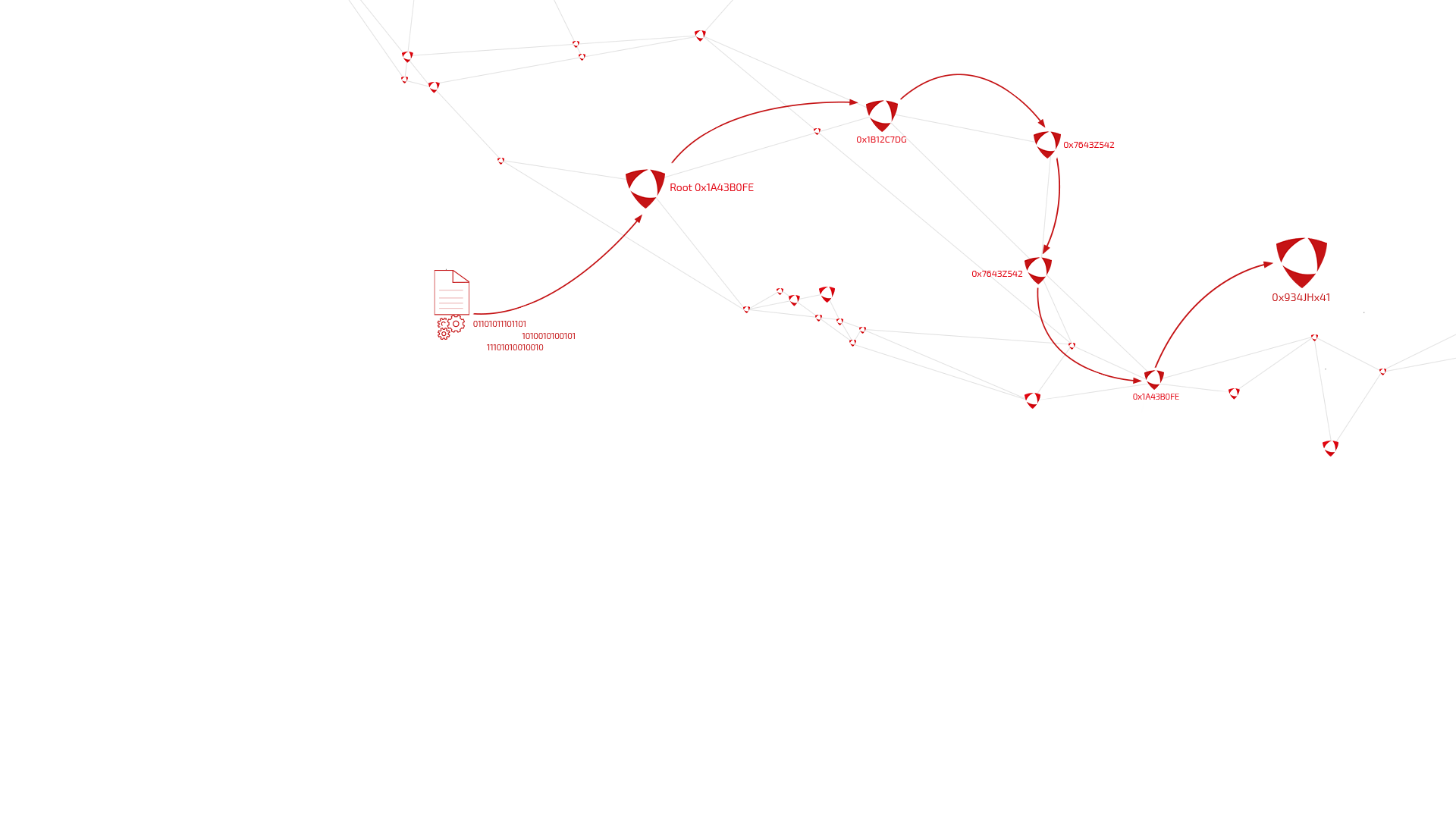
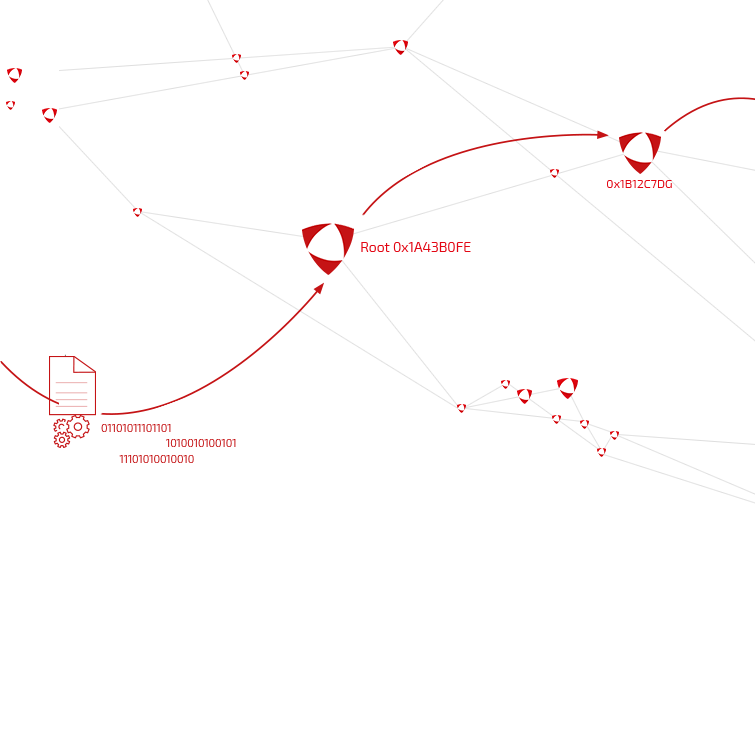
NVD is based on decentralized, cryptographic access control. Data content remains invisible to unauthorized parties and can only be decrypted and reconstructed if the calculation paths are correct. This allows sensitive information to be securely used in defense scenarios, medical data to be shared in a controlled manner, or IoT devices to be integrated without risk. The data owner decides whether access is permanent, time-limited, or tied to attributes such as hardware or location.

With Full Control
With NVD, data can be shared without losing control.
Every release is made via a Share ID, which only opens the entry point into the encryption chain. No permanent keys are in circulation – access can be revoked at any time.
This fundamentally distinguishes NVD from previous solutions: those who share data no longer lose sovereignty over it. Access can be flexibly linked to attributes such as time, location, or user groups.
At the same time, usage remains efficient: despite encryption, data can be compressed and used without redundant copies. The result: secure applications by default, integrable into any infrastructure – from military environments to healthcare, industry, and administration.
Our Offer:
Security by Default
You understand your business best. Therefore, we focus on empowering you so that
- Your data is protected at all times,
- You always maintain full control over your data, even when sharing it with third parties,
- without having to deal with complex security or cryptography procedures.
To make our goal tangible for you, we use a simple example: Today, we naturally drive a car with brakes, seatbelts, and airbags.
Our goal is to ensure that all data applications become ‘secure by default’ in the same natural way.
Through our API, your application developers can transform existing solutions into secure applications with minimal additional effort.
Because for us, data security should be as self-evident as a car’s brakes.
Contact Us
Please feel free to contact us at: